Set up Phone Risk
Learn how to set up Socure Phone Risk in the RiskOS™ Dashboard to assess the fraud risk of phone numbers and confirm their link to consumer identities.
Before you start
Make sure you have the following:
Your account owner or administrator can enable this for you. If you're unsure who to contact, reach out to support for assistance.
If this is your first time working with workflows, review the Workflow overview to understand inputs, enrichments, routing logic, and decisions.
How it works
Socure Phone Risk evaluates a phone number and returns signals to help assess phone-related fraud risk and identity consistency.
Phone Risk returns:
- Phone Risk Score: Indicates the relative risk associated with a phone number.
- Name–Phone Correlation: Indicates how strongly a phone number aligns with the individual’s name.
These signals can be used across onboarding, authentication, profile updates, and higher-risk transactions to support fraud prevention and trust decisions.
Phone Risk with SIM Swap
Phone Risk can be configured to include the Real-Time SIM Swap Verification service, which help identify recent changes to a phone number’s SIM that may indicate elevated account takeover or fraud risk.
As part of the account setup process, organizations must also specify the desired time window for SIM swap validation. By default, this period is set to the last 48 hours, but it can be configured to any timeframe from the past 1 hour up to no maximum limit. Organizations can adjust the SIM swap validation period as needed over time.
For example, if the SIM swap period is set to 48 hours, RiskOS™ will check whether a SIM swap occurred for the given phone number within the last 48 hours.
Note:
The SIM swap validation setting is enabled by Socure and cannot be manually configured. If it needs to be changed, contact your Account Manager.
It is important to choose an appropriate validation period. If the period is too short, you may miss a SIM swap event. Conversely, if the period is too long, the event may no longer be relevant, as the end user may have already detected the fraud, contacted their carrier, and regained control of their SIM.
How Phone Risk fits into a workflow
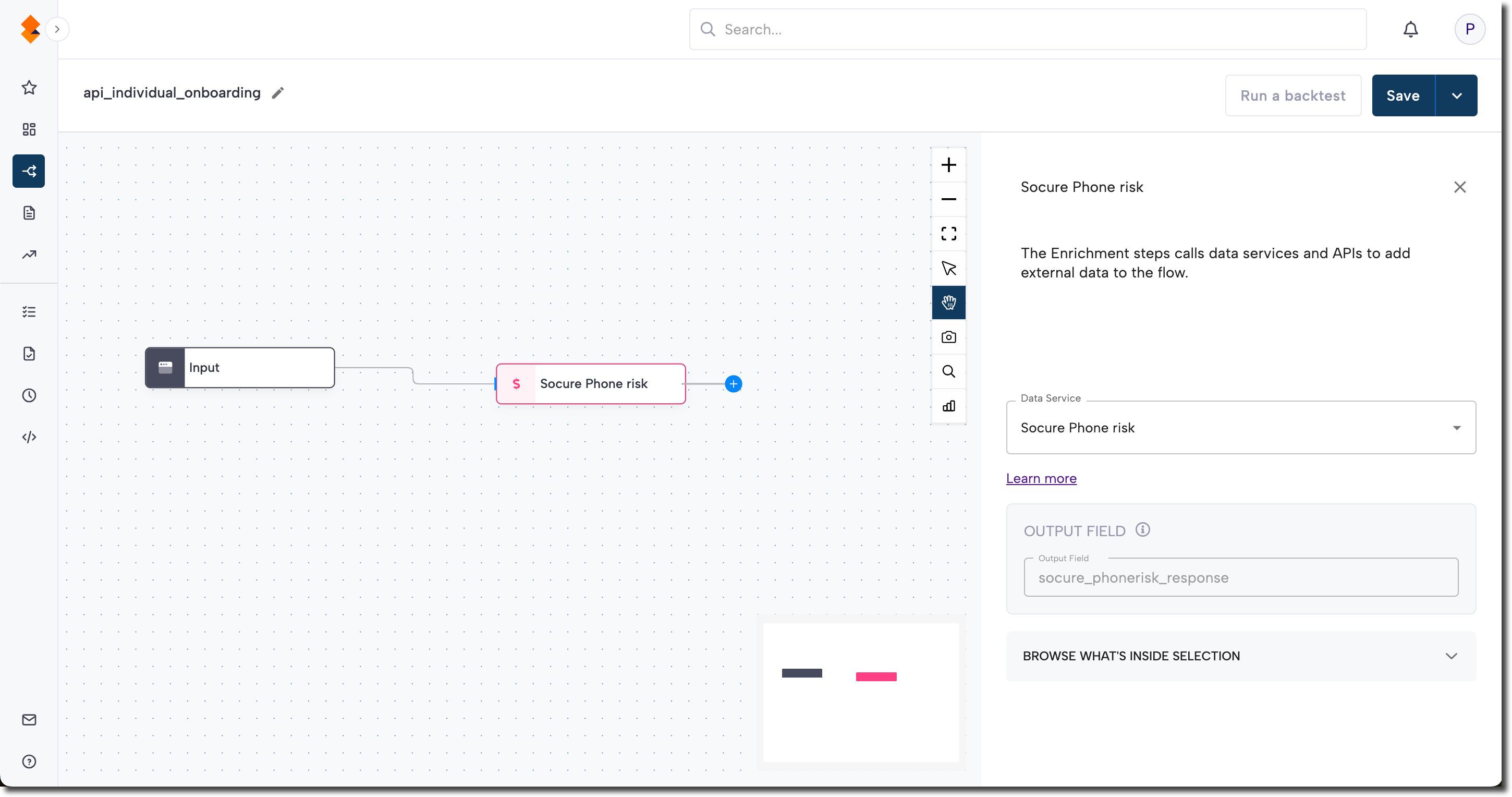
In RiskOS™, workflows are built by connecting reusable components. Phone Risk is added as an Enrichment step.
Once the enrichment runs, its outputs are available to downstream workflow components, such as:
- Conditions
- Decision rules
- Rule score cards
- Manual review steps
- Final decisions
For more detail on these components, see Workflow Steps.
Execution flow in RiskOS™
Phone Risk runs synchronously as part of a RiskOS™ workflow. There is no user handoff or pause in execution.
flowchart LR
A[Input]
B[Phone Risk]
C[Routing logic]
D[Decision]
A --> B --> C --> D
At a high level, the execution flow looks like this:
- Input:
You call the Evaluation API with a phone number and supporting identity data. - Phone Risk enrichment:
RiskOS™ evaluates the phone number and (optionally) SIM swap status. - Routing logic:
The workflow evaluates Phone Risk scores, correlations, and reason codes. - Decision:
The workflow returns a final outcome (for example,Accept,Review, orReject).
Workflow components used by Phone Risk
Phone Risk uses a subset of standard RiskOS™ workflow components.
| Component | Purpose | Typical input | Output / What to use next |
|---|---|---|---|
| Input | Start an evaluation | Phone number, country, supporting identity data | Workflow execution begins |
| Enrichment | Evaluate phone risk | — | Risk score, correlation, reason codes |
| Condition | Branch based on risk or signals | Phone risk score, SIM swap indicators | Route to appropriate path |
| Decision Rule / Score Card | Apply policy or scoring logic | Phone risk signals | Pass/fail or cumulative risk classification |
| Decision | Emit final outcome | Routed value | Accept / Review / Reject |
Configure Phone Risk
Add Phone Risk to a workflow
- In the RiskOS™ Dashboard, go to Workflows and create a new workflow or open an existing one.
- On the workflow canvas, select the plus (+) icon.
- Add an Enrichment step and choose one of the following:
- Phone Risk
- Phone Risk with SIM Swap
After the enrichment is added, its outputs can be referenced by downstream workflow logic.
Configure inputs and routing
Phone Risk evaluates the phone number and supporting identity information provided by your workflow. Providing complete and accurate inputs improves overall signal quality.
You can use Phone Risk outputs—including scores, correlations, and reason codes—to configure routing logic that supports outcomes such as Accept, Review, or Reject.
Routing strategies should align with your organization’s fraud policy and risk tolerance.
Save and publish
Once your workflow is configured, publish it to go live.
Workflow testing checklist
Use this checklist to confirm accuracy, resilience, and completeness of the workflow before going live.
Updated about 1 month ago
