Ashby Integration — Seamless Setup in Under 10 Minutes
Ashby customers have a packaged, customizable workforce verification solution available in RiskOS™ for instant identity and document verification in your hiring workflows. Socure has integrated with Ashby in a way that requires no engineering effort on Ashby customer's side.
This guide walks Ashby customers through configuring Socure's workforce verification solution via webhooks in Ashby. All you need to do is configure webhooks in Ashby. RiskOS™ will then, automatically initiate workforce verification workflow and apply a tag (e.g. HIGH_RISK_IDENTITY or LOW_RISK_IDENTITY) to the candidate profile in Ashby. RiskOS™ Case Management will have all the insights including model scores, reason code and Gen AI powered explanations to explain the "why" behind the decision.
Configure webhooks for Top of Funnel Passive Checks (5 Minutes)
Retrieve your Customer ID from the Developer Workbench in RiskOS™.
- Set the Webhook type to Application Submitted
- Enter the Request URL
- Enter the Secret Token
- Enable the webhook
Configure webhooks for Bottom of Funnel Document Verification (5 Minutes)
Retrieve your Customer ID from the Developer Workbench in RiskOS™.
- Set the Webhook Type to Candidate Hired
- Enter the Request URL
- Enter the Secret Token
- Enable the webhook
Configure Ashby to capture candidate consent or other legal requirements (5 Minutes)
Use a required question for any necessary legal language or links to documents (e.g., a candidate privacy policy) or to collect any required consents for workforce verification. For example, you may require a user to answer "I Consent" before submission. Please consult with your legal team for any specific requirements.
Before you start configuration
Make sure the following setup steps are complete:
| Step | Details |
|---|---|
| RiskOS™ Account | Your RiskOS™ account has been provisioned and workforce_verification workflow has been enabled. Your Socure Solution Consultant will be able to confirm. |
| Review workflow | Review workflow and adjust risk thresholds (as needed). workforce_verification workflow would have following modules included by default: Email Risk + Graph Intelligence, Phone Risk + Graph Intelligence, Sigma Identity Fraud + Graph Intelligence, Sigma Synthetic Fraud, Document Verification. You can add additional modules if desired and adjust risk thresholds as desired. |
How it works with Ashby
- Configure an Application Submitted webhook in Ashby to trigger passive checks in RiskOS™.
- RiskOS™ retrieves the following information from Ashby: Name (this is subsequently parsed as First Name and Last Name), Primary Phone Number, Primary Email, Physical Address (if available), IP Address
- RiskOS™ feeds the candidate information to a pre-configured workflow using Socure products such as Phone Risk, Email Risk, Sigma Identity Fraud, Sigma Synthetic Fraud, Graph Intelligence
- RiskOS™ evaluation includes model scores, reason codes and graph intelligence signals, which are fed into a decisioning logic, which drive one of two pre-configured tag values:
HIGH_RISK_IDENTITYorLOW_RISK_IDENTITY - RiskOS™ applies the tag to the applicant profile in Ashby (e.g.,
HIGH_RISK_IDENTITY,LOW_RISK_IDENTITY). - Configure a Candidate Hired webhook for document verification at the bottom of the funnel.
- RiskOS™ applies final document verification tags (
DOCUMENT_VERIFICATION_PASSED,DOCUMENT_VERIFICATION_FAILED,DOCUMENT_VERIFICATION_REVIEW).
Example workflow
sequenceDiagram participant Ashby participant RiskOS™ participant HR Ashby->>RiskOS™: Application Submitted webhook RiskOS™->>RiskOS™: Run Workforce Verification workflow RiskOS™->>Ashby: Apply HIGH_RISK_IDENTITY or LOW_RISK_IDENTITY tag HR->>RiskOS™: Review flagged cases Ashby->>RiskOS™: Candidate Hired webhook RiskOS™->>RiskOS™: Run Document Verification workflow RiskOS™->>Ashby: Apply final verification tag
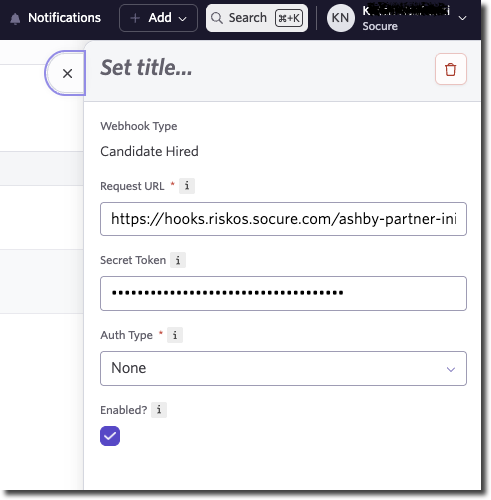
Configuring Ashby webhooks
Note:
Before you start, contact [email protected] to:
- Get a Request URL and Secret Token from Socure. You will use this to configure webhooks in Ashby.
- Share your Ashby API key with Socure. This is required to complete the configuration.
Application Submitted webhook (Top-of-Funnel Passive Checks)
- Sign in to Ashby as an Administrator.
- Navigate: Admin > Integrations > Webhooks.
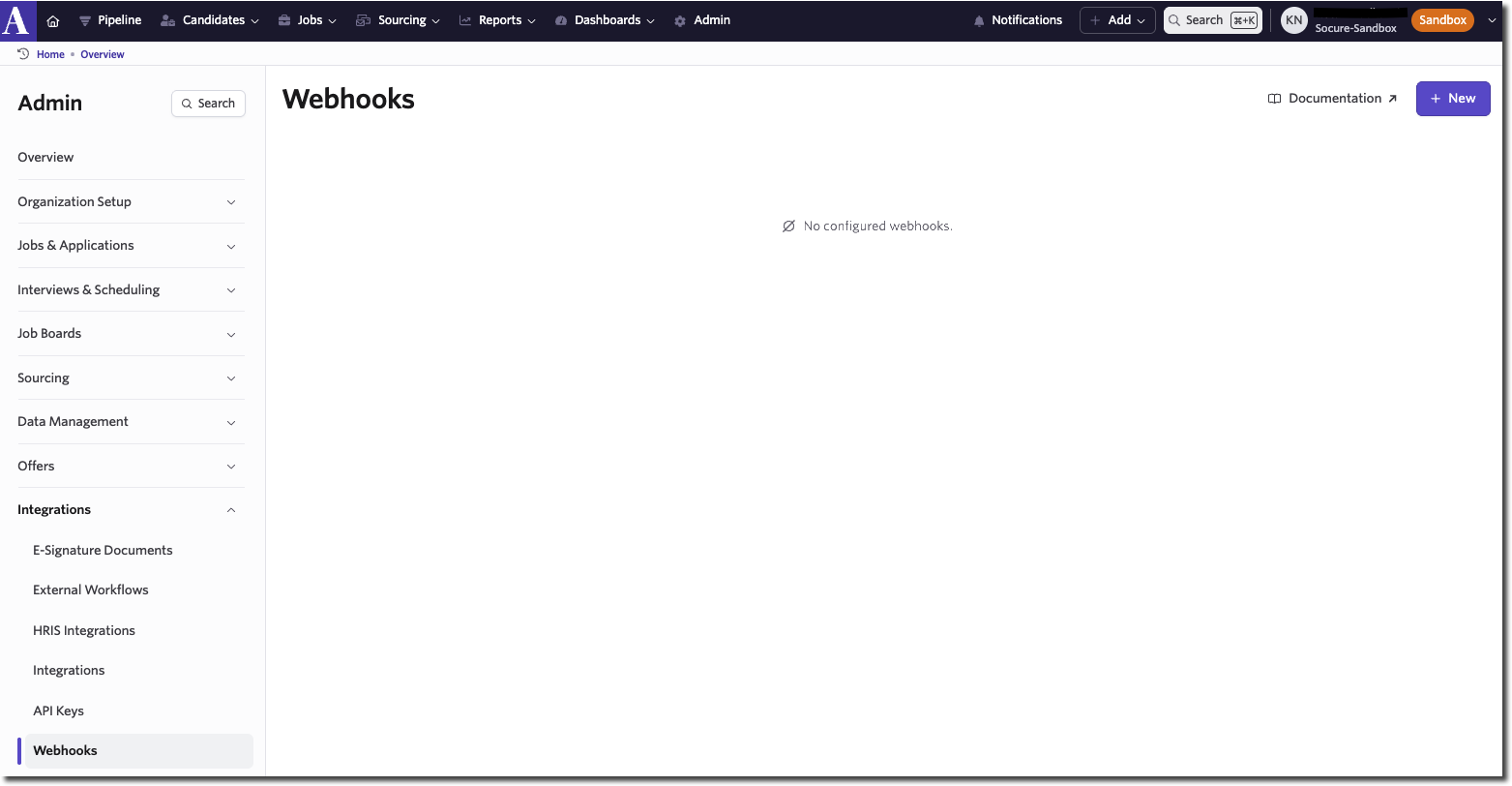
- Click + New to add a webhook and configure as follows:
| Field | Value |
|---|---|
| Webhook Type | Application Submitted |
| Request URL | https://hooks.riskos.socure.com/ashby-partner-init?accountId=<customerId> |
| Secret Token | Your secret token |
| Auth Type | None |
| Enabled | True (checked) |
customerId` is available in your RiskOS™ account under Developer Workbench → API Keys.
- You will now see the Application Submitted webhook on the Webhooks page.
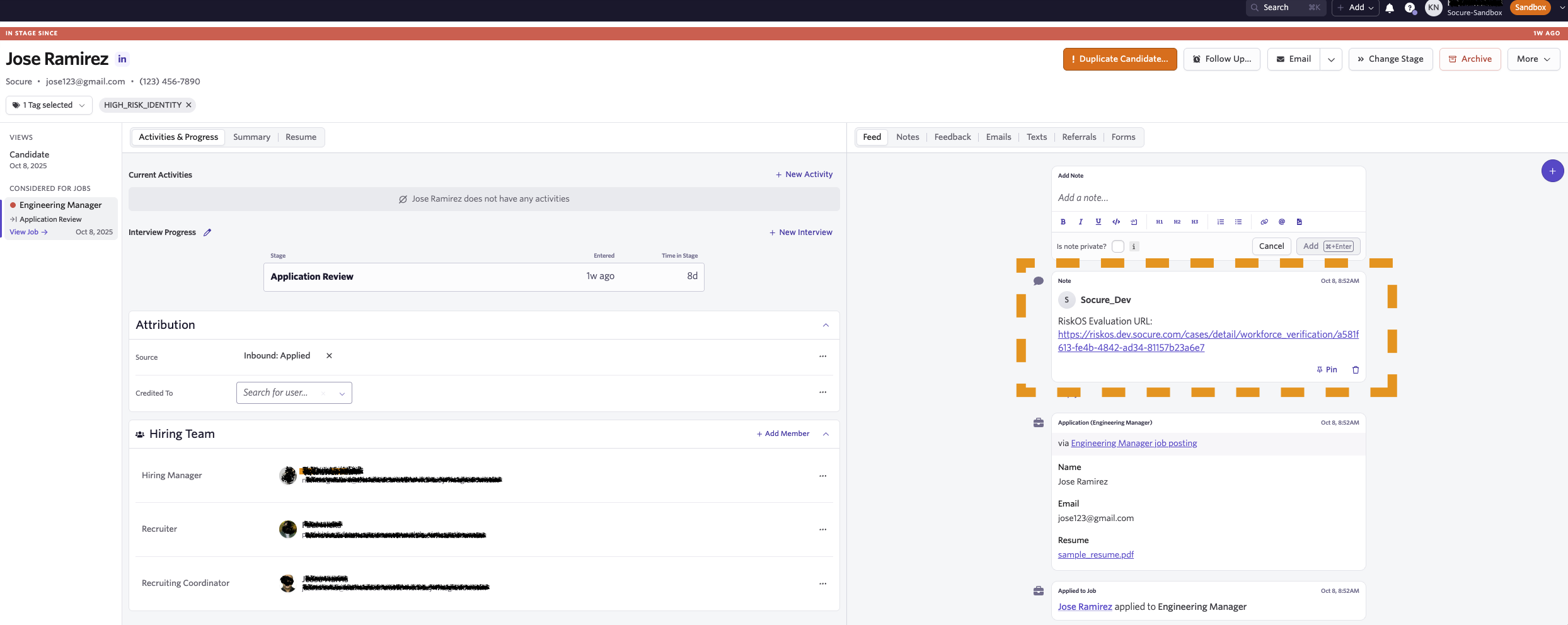
Once configured, RiskOS™ will append tags (HIGH_RISK_IDENTITY or LOW_RISK_IDENTITY) to the applicant profile.
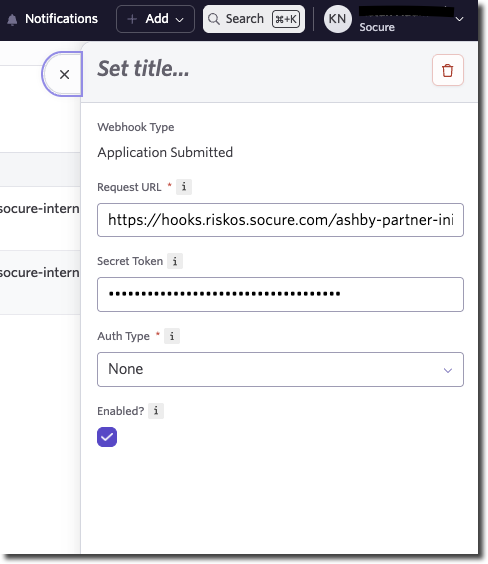
Candidate Hired webhook (Bottom-of-Funnel Document Verification)
Follow the same configuration steps as the Application Submitted webhook section above to add a second webhook with Webhook Type: Candidate Hired. RiskOS™ will append tags such as:
DOCUMENT_VERIFICATION_PASSEDDOCUMENT_VERIFICATION_FAILEDDOCUMENT_VERIFICATION_REVIEW
Case review in RiskOS™
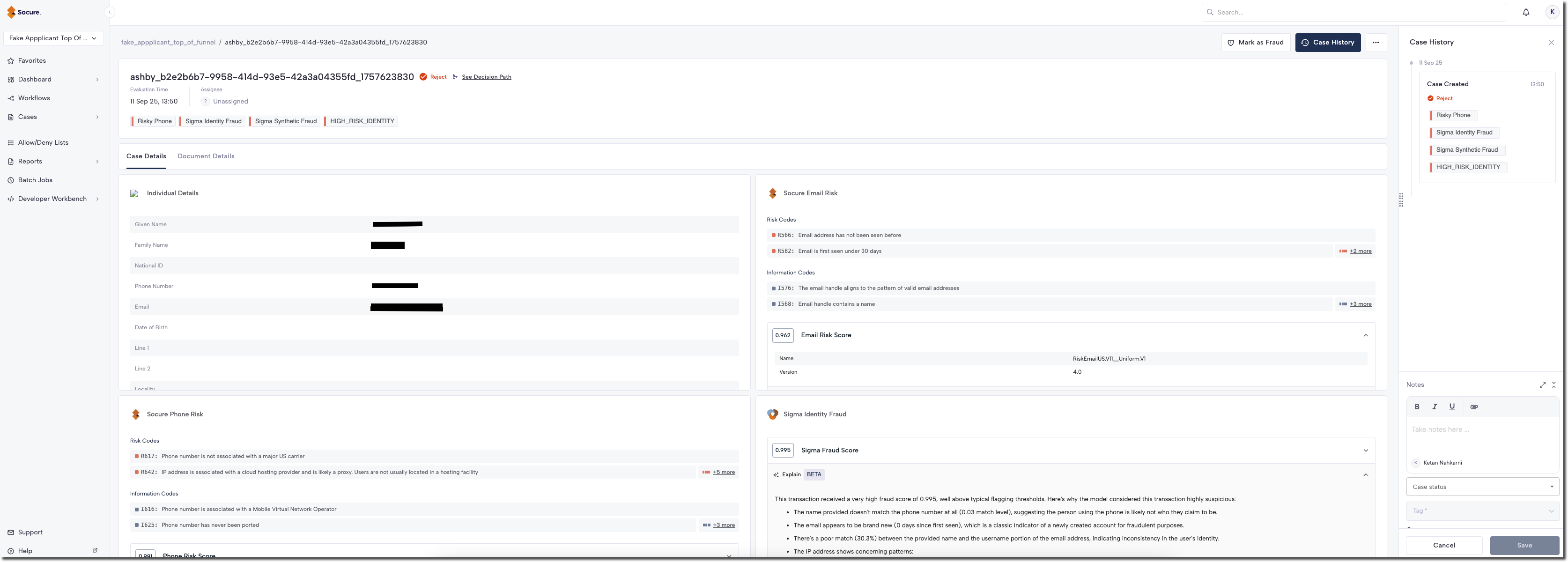
RiskOS™ offers a case management solution for flagged candidates. Review includes:
- Tags and decision logic
- Reason codes and model scores
- Gen AI explanations of risk signals
This helps your HR team understand why a candidate was flagged and supports compliance/audit readiness.
Best practices for integration and maintenance
- Validate webhook configurations and test with sample applicants.
- Use RiskOS™ sandbox mode for safe testing before production rollout.
- Escalate issues with
eval_id, webhook payload, and context to Socure Support. - Log applicant evaluations, decision tags, and errors for auditability.
Validation checklist
Webhook events
Schema + error handling
Logging + observability
Next steps
Once webhooks are configured, test the integration by submitting a test application or hiring a test candidate in Ashby. Confirm RiskOS™ applies the expected tags (HIGH_RISK_IDENTITY, DOCUMENT_VERIFICATION_PASSED, etc.).
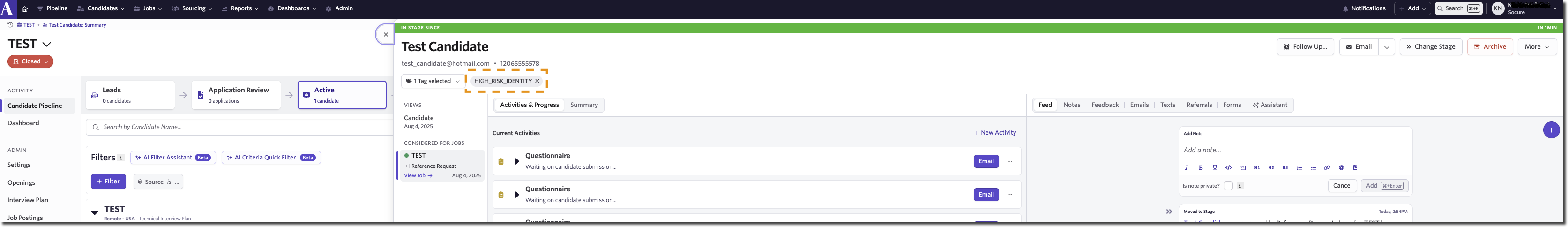
RiskOS™ also adds a note to the candidate profile with a deep link to the RiskOS™ case. HR Team Members can click through the link e.g. https://riskos.socure.com/cases/detail/workforce_verification/a581f613-fe4b-4842-ad34-81157b23a6e7 to access the case details using RiskOS™ Case Management. NOTE: The HR Team member will need to be added as a RiskOS™ user from Users page.
RiskOS™ provides a robust Case Management solution empowering reviewers and analysts to make confident decisions about the cases they investigate. Each case provides detailed insights including model scores, reason codes and workflow decisions. Not only that, GenAI Explainability brings natural-language explanations to the key outputs across Socure's platform—surfacing the "why" behind risk scores, identity match decisions, and document verification results.
Updated about 1 hour ago
