Set up Digital Intelligence
Learn how to set up Socure Digital Intelligence in the RiskOS™ Dashboard to evaluate device and behavioral risk.
Before you start
Make sure you have the following:
Your account owner or administrator can enable this for you. If you're unsure who to contact, reach out to support for assistance.
If this is your first time working with workflows, review the Workflow overview to understand inputs, enrichments, routing logic, and decisions.
How it works
Socure Digital Intelligence evaluates device attributes, behavioral signals, network characteristics, and historical profiling data collected across Socure’s client consortium.
Digital Intelligence helps you:
- Identify high-risk devices and networks
- Detect anomalous behavior patterns
- Leverage historical Entity Profiler insights tied to phone numbers, email addresses, or national IDs
- Apply consistent risk scoring across digital interactions
These signals are typically evaluated using Rule Score Cards to produce an overall Digital Intelligence risk score.
How Digital Intelligence fits into a workflow
In RiskOS™, workflows are built by connecting reusable components. Digital Intelligence is added as an Enrichment step and is commonly evaluated using Rule Score Cards.
Once the enrichment runs, its outputs are available to downstream workflow components, including:
- Rule score cards
- Conditions
- Decision rules
- Manual review steps
- Final decisions
For more detail on these components, see Workflow Steps.
Execution flow in RiskOS™
Digital Intelligence runs synchronously as part of a RiskOS™ workflow. There is no user handoff or pause in execution.
flowchart LR
A[Input]
B[Digital Intelligence]
C[Score card evaluation]
D[Decision]
A --> B --> C --> D
At a high level, the execution flow looks like this:
-
Input
You call the Evaluation API with identity, device, and digital interaction attributes. -
Digital Intelligence enrichment
RiskOS™ evaluates device, behavioral, network, and Entity Profiler signals. -
Score card evaluation
Rule Score Cards evaluate Digital Intelligence signals to generate an overall risk score. -
Decision
The workflow returns a final outcome (for example, Accept, Review, or Reject).
Workflow components used by Digital Intelligence
Digital Intelligence uses a subset of standard RiskOS™ workflow components.
| Component | Purpose | Typical input | Output / What to use next |
|---|---|---|---|
| Input | Start an evaluation | Identity, device, and interaction data | Workflow execution begins |
| Enrichment | Collect digital risk signals | — | Device, network, behavioral signals |
| Rule Score Card | Aggregate digital risk | Digital Intelligence signals | Overall risk score |
| Condition | Branch based on score thresholds | Digital Intelligence score | Route to appropriate path |
| Decision | Emit final outcome | Routed value | Accept / Review / Reject |
Configure Digital Intelligence
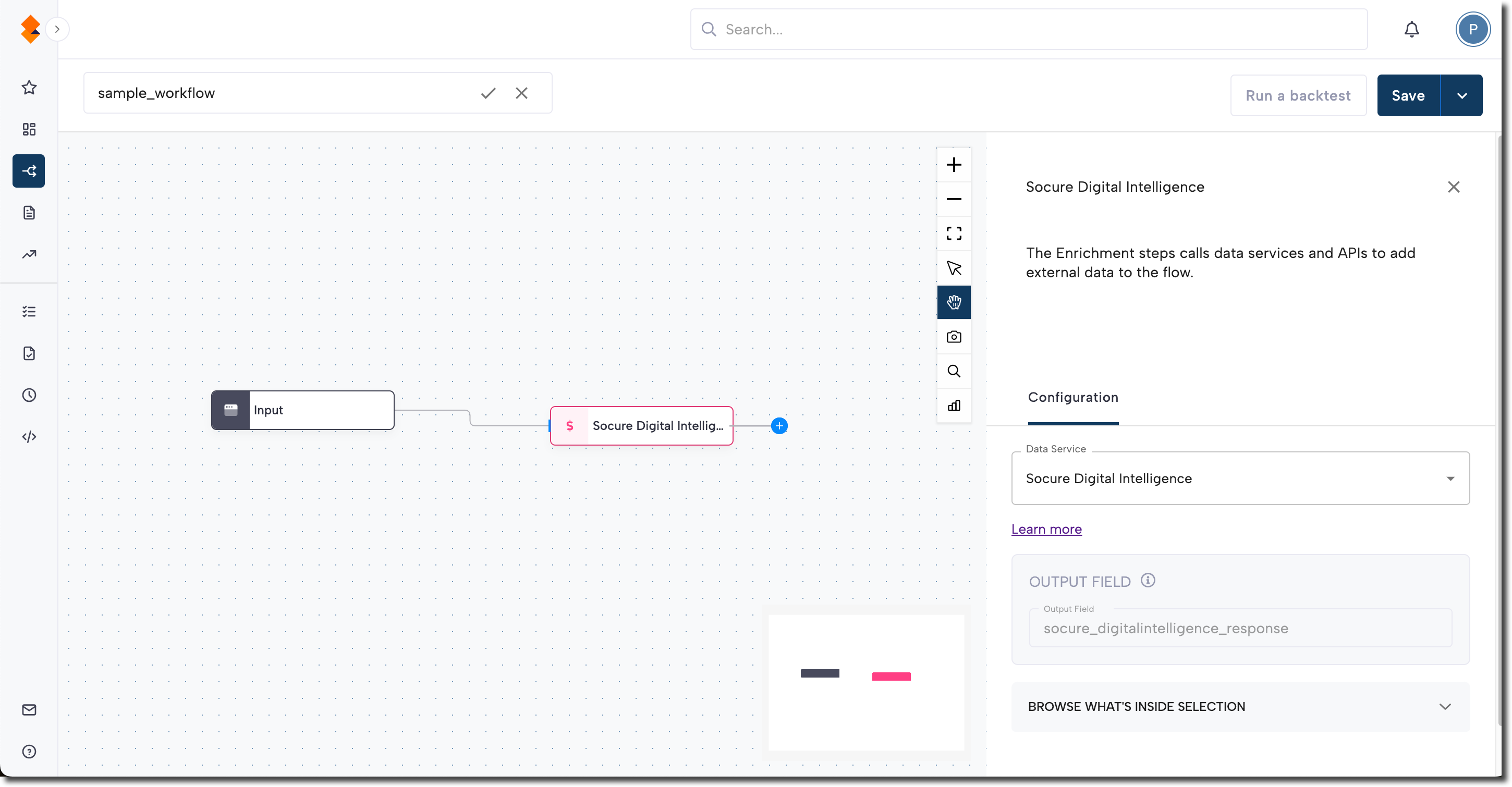
Add Digital Intelligence to a workflow
- In the RiskOS™ Dashboard, go to Workflows and create a new workflow or open an existing one.
- On the workflow canvas, select the plus (+) icon.
- Add an Enrichment step and select Socure Digital Intelligence.
After the enrichment is added, its outputs can be referenced by score cards and downstream workflow logic.
Configure Digital Intelligence score cards
Digital Intelligence is typically evaluated using Rule Score Cards.
Your Socure Solution Consulting team will assist with initial score card configuration. Digital Intelligence commonly uses multiple score cards covering:
- Device attributes
- Network and behavioral signals
- Entity Profiler insights for phone number, email address, or national ID
These score cards work together to produce an overall Digital Intelligence risk score.
Common decision patterns include:
- High risk → Reject immediately
- Medium risk → Step up verification or manual review
- Low risk → Accept or continue workflow evaluation
For more details, see RiskOS™ Score Card: Digital Intelligence Example.
Save and publish
Once your workflow is configured, publish it to go live.
Workflow testing checklist
Use this checklist to confirm accuracy, resilience, and completeness before going live with your Digital Intelligence implementation.
Updated about 1 month ago
