Set up eCBSV
Learn how to set up eCBSV in the RiskOS™ Dashboard to validate a user's name, date of birth, and Social Security number (SSN) directly with the Social Security Administration (SSA).
Before you start
Make sure you have the following:
To activate eCBSV, the following steps must be completed:
Your Socure Account Manager and Solutions Consultant will guide you through this process.
How it works
Socure connects directly to the SSA so you don’t have to. RiskOS™ submits verification requests on your behalf and returns results in a format that can be used directly within your workflows.
eCBSV returns:
- Confirmation of whether the provided SSN matches the supplied name and date of birth
- An indicator if the SSN belongs to a deceased individual
Responses include reason codes that can be used to drive routing and decisioning logic.
How eCBSV fits into a workflow
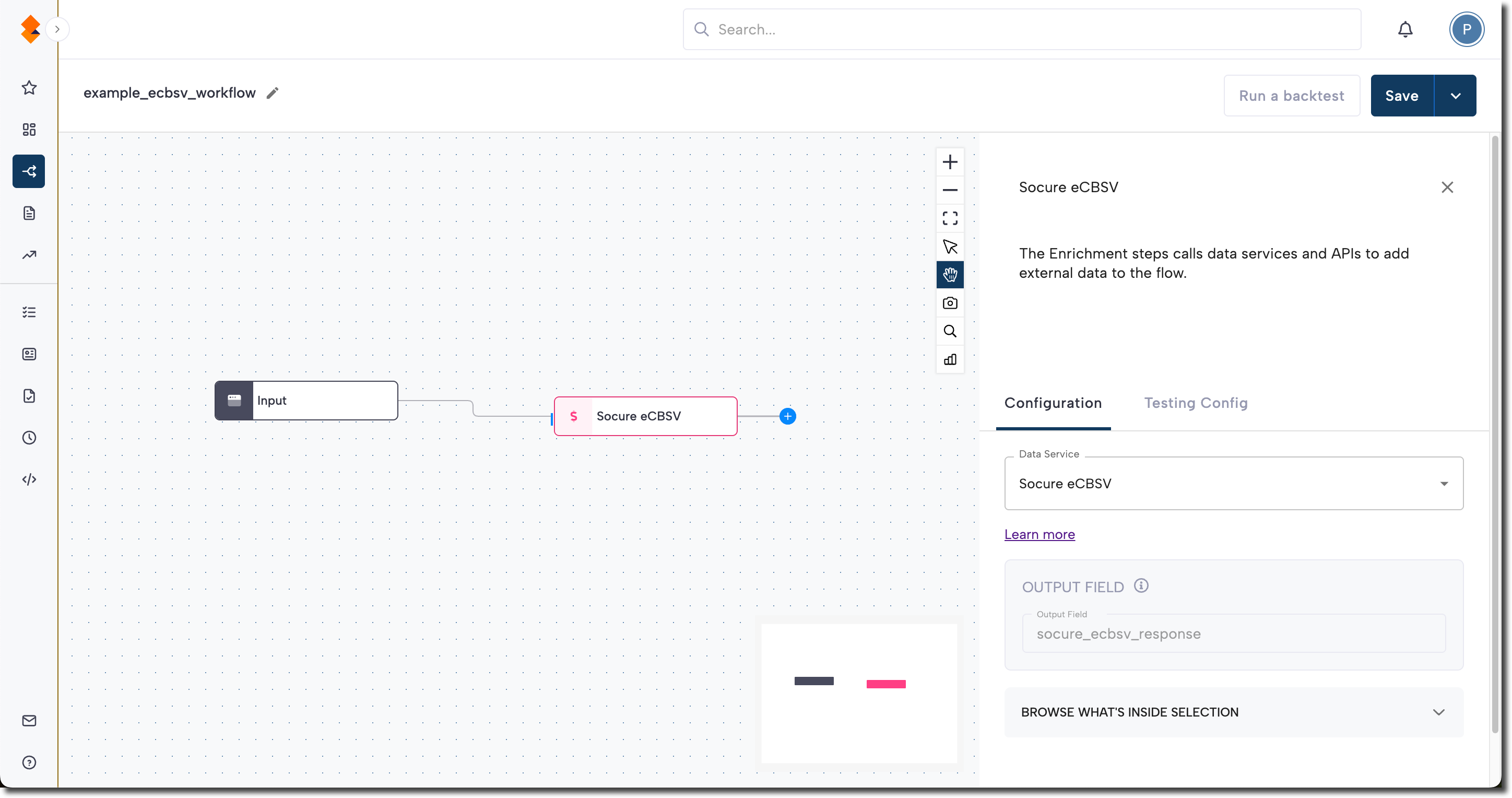
In RiskOS™, workflows are built by connecting reusable components. eCBSV is added as an Enrichment step.
Once the enrichment runs, its outputs are available to downstream workflow components, including:
- Conditions
- Decision rules
- Rule score cards
- Manual review steps
- Final decisions
For more detail on these components, see Workflow Steps.
Execution flow in RiskOS™
eCBSV runs synchronously as part of a RiskOS™ workflow. There is no user handoff or pause in execution once consent has been collected.
flowchart LR
A[Input]
B[eCBSV]
C[Routing logic]
D[Decision]
A --> B --> C --> D
At a high level, the execution flow looks like this:
-
Input
You call the Evaluation API with name, date of birth, SSN, and a user consent indicator. -
eCBSV enrichment
RiskOS™ submits the verification request to the SSA and returns match results and reason codes. -
Routing logic
The workflow evaluates match, no-match, or ambiguous responses. -
Decision
The workflow returns a final outcome (for example, Accept, Review, or Reject).
Workflow components used by eCBSV
eCBSV uses a subset of standard RiskOS™ workflow components.
| Component | Purpose | Typical input | Output / What to use next |
|---|---|---|---|
| Input | Start an evaluation | Name, DOB, SSN, user consent | Workflow execution begins |
| Enrichment | Verify identity with SSA | — | Match status, reason codes |
| Condition | Branch based on match results | eCBSV outputs | Route to appropriate path |
| Decision Rule / Score Card | Apply policy logic | eCBSV signals | Pass/fail or escalation |
| Decision | Emit final outcome | Routed value | Accept / Review / Reject |
Configure eCBSV
Add eCBSV to a workflow
- In the RiskOS™ Dashboard, go to Workflows and create a new workflow or open an existing one.
- On the workflow canvas, select the plus (+) icon.
- Add an Enrichment step and select eCBSV.
Configure inputs and routing
Common required inputs include:
given_namefamily_namedobnational_id(SSN)userConsent
You can configure routing logic to support both:
Upfront verification
Some organizations call eCBSV early in the workflow to validate SSA records before evaluating other signals.
Considerations:
- A match confirms individual field alignment with SSA records
- It does not confirm that the identity is cohesive or trustworthy
- SSA match tolerances are permissive and may allow synthetic combinations to pass
Step-up verification
More commonly, eCBSV is used later in the workflow to validate identities with:
- Low confidence scores
- Conflicting or anomalous signals
Save and publish
Once your workflow is configured, publish it to go live.
Workflow testing checklist
Use this checklist to confirm accuracy, resilience, and completeness of the workflow before going live.
userConsent: true is included in all live payloadsUpdated about 1 month ago
